Setting up the AWS KMS. Contributors Download PDF of this page. If you want to use Amazon encryption with Cloud Volumes ONTAP, then you need to set up the AWS Key Management Service (KMS). Ensure that an active Customer Master Key (CMK) exists. AWS Key Management Service (AWS KMS) is a managed service that makes it easy for you to create and control customer master keys (CMKs), the encryption keys used to encrypt your data.
- Latest Version Version 3.37.0. Published 2 days ago. Published 10 days ago. Published 17 days ago. Published 24 days ago.
- Using AWS KMS via the CLI with a Symmetric Key. Off the back of local-kms, I've been getting a few questions regarding how to interact with it via the CLI.So here are a few examples of how you can use AWS KMS (or local-kms) via the CLI.
March 12, 2021
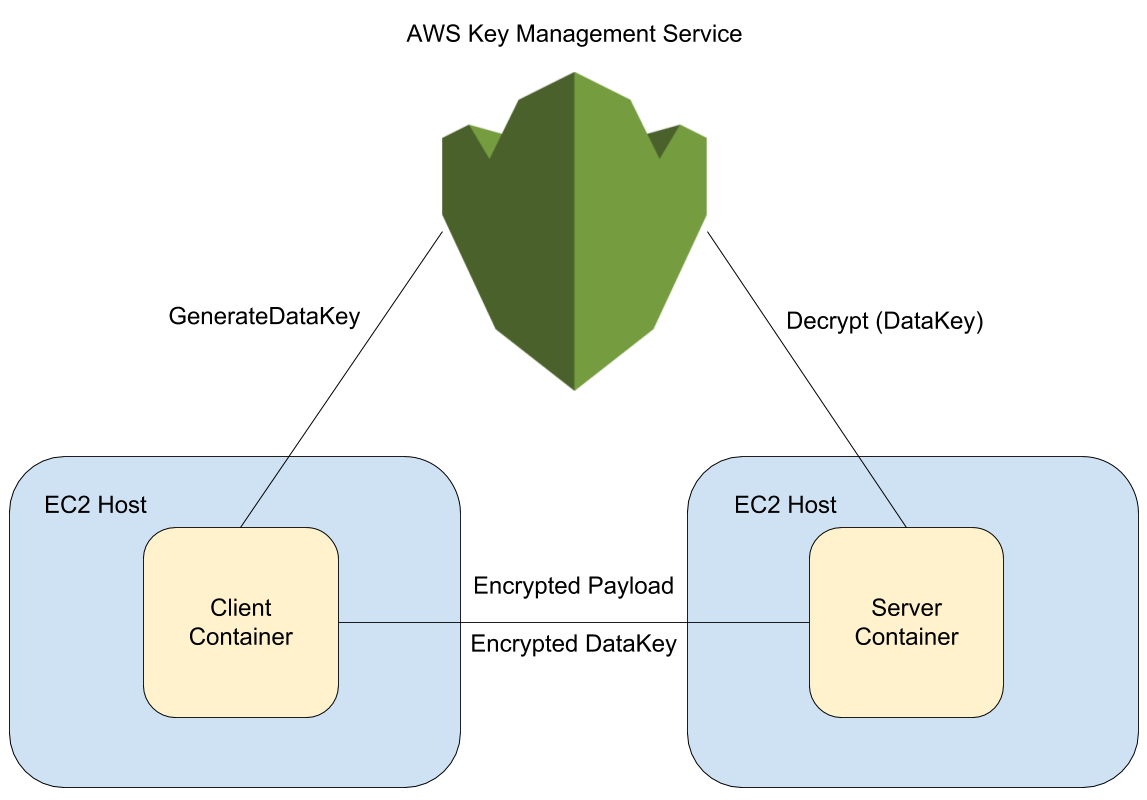
AWS KMS is an incredible offering by AWS that manages encryptionkeys, automatic rotation and secure storage. With rotation enabled,AWS will generate a new encryption key once a year without deletingthe previous keys. Any cipher generated by old keys can still bedecrypted. We don’t have access to the actual key, which meanswe can’t leak it.
Laravel ships an Encrypter class that uses AES for encryption.Replacing Laravel’s implementation with KMS takes only a simpleKmsEncrypter and a Service Provider.
The Service Provider
I just sent out a pull request to introduce a StringEncrypterinterface into Laravel so that this process can be simplified.https://github.com/laravel/framework/pull/36578
The Service Provider can look like this:
Notice how we’re instantiating a KmsClient inside the KmsEncrypterfactory callback. That gives us the chance of delegating howwe should resolve KmsClient to a separate process. One wayof doing that could be like this:
KmsEncrypter
Here’s how KmsEncrypter would look like:
Let’s dissect this class. First we have the KmsClient thatalready carries every configuration necessary to interactwith AWS KMS. Whether you use environment variable with AWSCredentials or let your AWS service assume role with permissionto interact with KMS, AWS SDK will handle the authentication.Then we have the key which should be the ARN of the AWS KMS keyor Alias of the key to be used. Finally we have context. Contextis a non-secret information (e.g. it will be plain text on CloudTrail)that allows you to bind your encryption with a specific signingcontext. If the exact same context is not provided when tryingto decrypt a specific cipher text, then the decryption will notwork. For instance, you may choose to use your service name asthe context of your encryption so that if other services accidentallytries to decrypt your cipher texts, it won’t just work. The developerwould have to make a conscious decision to specify another service’scontext when trying to decrypt cross-service data.
For ease of use, we can base64_encode() the cipher text and thenbase64_decode before decryption so that it’s easier to passthe data around. If you’re interested in learning more aboutbase64_encode, check out my post on Should I encrypt, hash or encode?.
Eloquent
Since the ServiceProvider is replacing the binding behind encrypteron Laravel’s service provider, we’re free to use Eloquent’scast feature to encrypt/decrypt attributes automatically.
This way whenever we try to save something into the password orclient_secret attributes, Eloquent will use KmsEncrypter toencrypt the data being stored and when we’re accessing the attribute,Eloquent Mutators will kick in and decrypt it.
Tests
For my automation tests, I decided to use a NullEncrypter implementationso that I don’t need to integrate directly with AWS KMS to runtests. Here’s how a NullEncrypter could look like:
On test could, we could then replace the binding like this:
Watch out for your storage service
During the development of this implementation, I first wrote a produtfeature without encryption and handed the APIs over to the frontendteam so that they could get started. I then started implementingAWS KMS encryption. I noticed that anytime my code would try todecrypt a cipher text, it would throw an exception saying
The reason I was getting this error was not because of the keynor the context. It was actually because I was interacting witha legacy database with strict=false and a password field oftype varchar(191). What would then happen was that the cipher textwould go above 191 characters and MySQL would truncate the datadown to 191 characters. Losing part of a cipher text means thatwe did not guarantee the integrity of the message and we canno longer decrypt it. Increasing the field size mitigated theissue.
Why don’t we inform the key to the decrypt API call to AWS?
When AWS encrypts a payload, it puts inside the cipher text anidentifier for which key was used for encryption. That way evenif we don’t know which key was used for encryption, AWS can stilldecrypt it as long as you have the complete cipher text and thecontext. This probably facilitates AWS’s job when rotating keys.When the key reaches 1 year of life, AWS will generate a brand newone and start using it for any new encryption. It won’t get ridof the old key, though. So if you make an API call asking fordecryption with a cipher text older than 1 year, AWS can stillfind the identifier for the key used and decrypt it.
Defining a Key with CloudFormation
The following template defines a MyEncryptionKey resource anda MyEncryptionKeyAlias resource. It will also output the aliasalongside the Key ARN. The Key ARN can be used to attach to an IAMRole that will need kms:Encrypt* and kms:Decrypt*. The Aliascan be used as an Environment Variable for your compute resourceso that it can be accessed by Laravel and injected into theKmsEncrypter class.
Conclusion
AWS KMS offering is great for the enterprise world. We will neverleak keys, they will be rotated automatically and it costs penniesfor the benefit that they bring. Laravel’s Encrypter and StringEncrypterinterfaces makes it easy to swap the implementation and offer agreat DX to work with encryption be it directly or via Eloquent.All in all it’s a great service, easy to use and designed to offersafety.
It’s important to note that I’m not rolling my own encryption here.I’m swapping Laravel’s Encrypter class with one that uses AWS KMS.In other words, AWS KMS is responsible for encryption/decryptionof the data and we should never roll our own encryption algorithms.
Follow me on Twitter tostay tuned with my latest work.
Cheers.
Marco Aurélio Deleu
Writing bad code for 10 years. Passionate about Laravel and AWS.
Easily create and control the keys used to encrypt or digitally sign your data
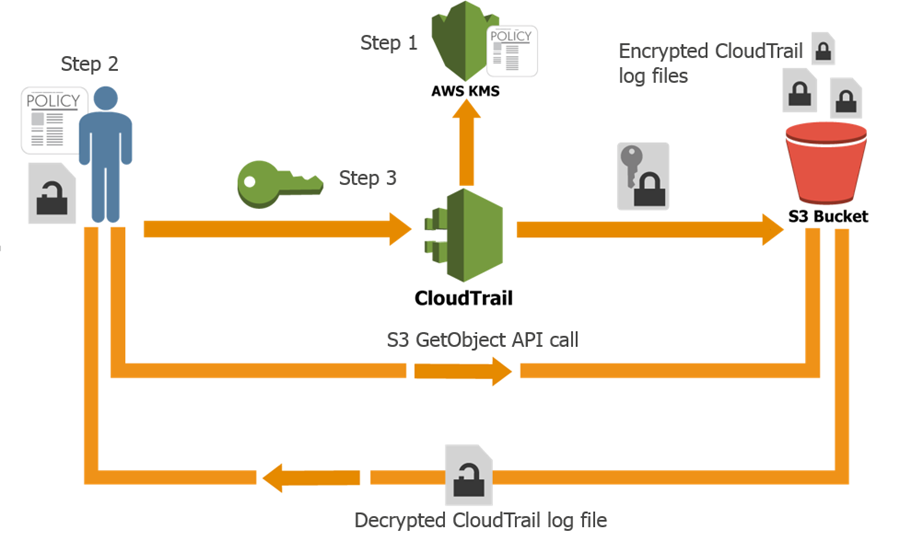
AWS Key Management Service (KMS) makes it easy for you to create and manage cryptographic keys and control their use across a wide range of AWS services and in your applications. AWS KMS is a secure and resilient service that uses hardware security modules that have been validated under FIPS 140-2, or are in the process of being validated, to protect your keys. AWS KMS is integrated with AWS CloudTrail to provide you with logs of all key usage to help meet your regulatory and compliance needs.
Try AWS Key Management Service
AWS Free Tier includes 20,000 free AWS Key Management Service requests each month.
Benefits
Fully managed
You control access to your encrypted data by defining permissions to use keys while AWS KMS enforces your permissions and handles the durability and physical security of your keys.

Centralized key management
AWS KMS presents a single control point to manage keys and define policies consistently across integrated AWS services and your own applications. You can easily create, import, rotate, delete, and manage permissions on keys from the AWS Management Console or by using the AWS SDK or CLI.
Learn more >>
Manage encryption for AWS services

AWS KMS is integrated with AWS services to simplify using your keys to encrypt data across your AWS workloads. You choose the level of access control that you need, including the ability to share encrypted resources between accounts and services. KMS logs all use of keys to AWS CloudTrail to give you an independent view of who accessed your encrypted data, including AWS services using them on your behalf.
Learn more >>
Encrypt data in your applications
AWS KMS is integrated with the AWS Encryption SDK to enable you to used KMS-protected data encryption keys to encrypt locally within your applications. Using simple APIs you can also build encryption and key management into your own applications wherever they run.
Learn more >>
Digitally sign data
AWS KMS enables you to perform digital signing operations using asymmetric key pairs to ensure the integrity of your data. Recipients of digitally signed data can verify the signatures whether they have an AWS account or not.
Learn more >>
Low cost
There is no commitment and no upfront charges to use AWS KMS. You only pay US $1/month to store any key that you create. AWS managed keys that are created on your behalf by AWS services are free to store. You are charged per-request when you use or manage your keys beyond the free tier.
Learn more >>
Secure
AWS KMS uses hardware security modules (HSMs) that have been validated under FIPS 140-2, or are in the process of being validated, to generate and protect keys. Your keys are only used inside these devices and can never leave them unencrypted. KMS keys are never shared outside the AWS region in which they were created.
Learn more >>
Compliance
The security and quality controls in AWS KMS have been certified under multiple compliance schemes to simplify your own compliance obligations. AWS KMS provides the option to store your keys in single-tenant HSMs in AWS CloudHSM instances that you control.
Learn more >>
Built-in auditing
AWS KMS is integrated with AWS CloudTrail to record all API requests, including key management actions and usage of your keys. Logging API requests helps you manage risk, meet compliance requirements and conduct forensic analysis.
Learn more >>
Blog posts & articles
Read about AWS Key Management Service security, compliance, and availability.
Learn moreInstantly get access to the AWS Free Tier.
Sign upGet started building with AWS Key Management Service in the AWS Console.
Aws Kms S3
Sign in