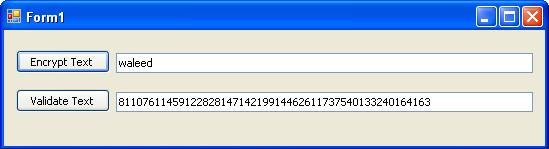
- In this example, we used the hashlib.md5 function to encode the string value into a hash value. We then used the hexdigest method to get the hexadecimal equivalent of the generated hash value. Similarly, we can also use the digest method to get the byte equivalent of the generated hash value. Example 5: Calculating MD5 hash of a file in.
- The MD5 algorithm is intended for digital signature applications, where a large file must be 'compressed' in a secure manner before being encrypted with a private (secret) key under a public-key cryptosystem such as RSA.' To calculate the MD5 hash of a file, use the md5file function.
- MySQL MD5 Calculates an MD5 128-bit checksum for a string. The value is returned as a binary string of 32 hex digits, or NULL if the argument was NULL. The return value can, for example, be used as a hash key.
This plugin easily encodes MD5 and SHA1 as well as encoding and decoding of Base64 and Xtea strings. But right now, we are interested in MD5. So to convert it into MD5, call '$.crypt' function and pass algorithm name which is 'md5' and value that needs to be encrypted.

Statistically speaking, for any string (and there is an infinite number), the MD5 associates for a given value a 128-bit fingerprint (a finite number of possibilities). It is therefore mandatory that there are collisions (2 strings with the same hash). Several research works on the subject have demonstrated that the MD5 algorithm, although creating a large entropy of data, could be attacked, and that it was possible to generate chains with the same fingerprints (after several hours of neat calculations).

Example: Discovered by Wang & Yu in How to break MD5 and other hash functions, the two hexadecimal values (the values and not the ASCII string) 4dc968ff0ee35c209572d4777b721587d36fa7b21bdc56b74a3dc0783e7b9518afbfa200a8284bf36e8e4b55b35f427593d849676da0d1555d8360fb5f07fea24dc968ff0ee35c209572d4777b721587d36fa7b21bdc56b74a3dc0783e7b9518afbfa202a8284bf36e8e4b55b35f427593d849676da0d1d55d8360fb5f07fea2 have the same hash: '008ee33a9d58b51cfeb425b0959121c9 (they only differ by 8 hexadecimal digits)
Since this publication in 2005, MD5 encryption is no longer considered cryptographically, giving way to its successors: SHA1 then SHA256.
-->This article describes how and why you can use the MD5 or SHA-1 cryptographic hash values to verify which file you installed on your computer.
Original product version: Windows 10 - all editions
Original KB number: 889768
Summary
When you apply the hashing algorithm to an arbitrary amount of data, such as a binary file, the result is a hash or a message digest. This hash has a fixed size. MD5 is a hashing algorithm that creates a 128-bit hash value. SHA-1 is a hashing algorithm that creates a 160-bit hash value.
Use FCIV to compute MD5 or SHA-1 cryptographic hash values

Md5 Base64 Encoding
You can use the File Checksum Integrity Verifier (FCIV) utility to compute the MD5 or SHA-1 cryptographic hash values of a file.
Md5 Encoding Python
To compute the MD5 and the SHA-1 hash values for a file, type the following command at a command line:
For example, to compute the MD5 and SHA-1 hash values for the Shdocvw.dll file in your %Systemroot%System32 folder, type the following command:
